Merkle–Damgård construction
In cryptography, the Merkle–Damgård construction or Merkle–Damgård hash function is a method of building collision-resistant cryptographic hash functions from collision-resistant one-way compression functions.[1]: 145 This construction was used in the design of many popular hash algorithms such as MD5, SHA-1 and SHA-2.
The Merkle–Damgård construction was described in Ralph Merkle's Ph.D. thesis in 1979.[2] Ralph Merkle and Ivan Damgård independently proved that the structure is sound: that is, if an appropriate padding scheme is used and the compression function is collision-resistant, then the hash function will also be collision-resistant.[3][4]
The Merkle–Damgård hash function first applies an MD-compliant padding function to create an input whose size is a multiple of a fixed number (e.g. 512 or 1024) — this is because compression functions cannot handle inputs of arbitrary size. The hash function then breaks the result into blocks of fixed size, and processes them one at a time with the compression function, each time combining a block of the input with the output of the previous round.[1]: 146 In order to make the construction secure, Merkle and Damgård proposed that messages be padded with a padding that encodes the length of the original message. This is called length padding or Merkle–Damgård strengthening.
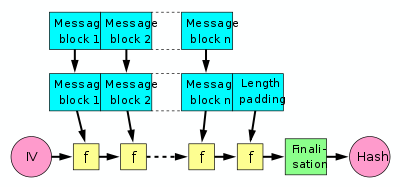
In the diagram, the one-way compression function is denoted by f, and transforms two fixed length inputs to an output of the same size as one of the inputs. The algorithm starts with an initial value, the initialization vector (IV). The IV is a fixed value (algorithm or implementation specific). For each message block, the compression (or compacting) function f takes the result so far, combines it with the message block, and produces an intermediate result. The last block is padded with zeros as needed and bits representing the length of the entire message are appended. (See below for a detailed length padding example.)
To harden the hash further, the last result is then sometimes fed through a finalisation function. The finalisation function can have several purposes such as compressing a bigger internal state (the last result) into a smaller output hash size or to guarantee a better mixing and avalanche effect on the bits in the hash sum. The finalisation function is often built by using the compression function.[citation needed] (Note that in some documents a different terminology is used: the act of length padding is called "finalisation".[citation needed])
Security characteristics[edit]
The popularity of this construction is due to the fact, proven by Merkle and Damgård, that if the one-way compression function f is collision resistant, then so is the hash function constructed using it. Unfortunately, this construction also has several undesirable properties:
- Second preimage attacks against long messages are always much more efficient than brute force.[5]
- Multicollisions (many messages with the same hash) can be found with only a little more work than collisions.[6]
- "Herding attacks", which combines the cascaded construction for multicollision finding (similar to the above) with collisions found for a given prefix (chosen-prefix collisions). This allows for constructing highly specific colliding documents, and it can be done for more work than finding a collision, but much less than would be expected to do this for a random oracle.[7][8]
- Length extension: Given the hash of an unknown input X, it is easy to find the value of , where pad is the padding function of the hash. That is, it is possible to find hashes of inputs related to X even though X remains unknown.[9] Length extension attacks were actually used to attack a number of commercial web message authentication schemes such as one used by Flickr.[10]
Wide pipe construction[edit]

Due to several structural weaknesses of Merkle–Damgård construction, especially the length extension problem and multicollision attacks, Stefan Lucks proposed the use of the wide-pipe hash[11] instead of Merkle–Damgård construction. The wide-pipe hash is very similar to the Merkle–Damgård construction but has a larger internal state size, meaning that the bit-length that is internally used is larger than the output bit-length. If a hash of n bits is desired, the compression function f takes 2n bits of chaining value and m bits of the message and compresses this to an output of 2n bits.
Therefore, in a final step a second compression function compresses the last internal hash value (2n bit) to the final hash value (n bit). This can be done as simply as discarding half of the last 2n-bit-output. SHA-512/224 and SHA-512/256 take this form since they are derived from a variant of SHA-512. SHA-384 and SHA-224 are similarly derived from SHA-512 and SHA-256, respectively, but the width of their pipe is much less than 2n.
Fast wide pipe construction[edit]

It has been demonstrated by Mridul Nandi and Souradyuti Paul that the Widepipe hash function can be made approximately twice as fast if the widepipe state can be divided in half in the following manner: one half is input to the succeeding compression function while the other half is combined with the output of that compression function.[12]
The main idea of the hash construction is to forward half of the previous chaining value forward to XOR it to the output of the compression function. In so doing the construction takes in longer message blocks every iteration than the original widepipe. Using the same function f as before, it takes n bit chaining values and n+m bits of the message. However, the price to pay is the extra memory used in the construction for feed-forward.
Parallel algorithm[edit]
The MD algorithm is inherently sequential. There is a parallel algorithm[13] which constructs a collision resistant hash function from a collision resistant compression function. The hash function PARSHA-256[14] was designed using the parallel algorithm and the compression function of SHA-256.
MD-compliant padding[edit]
As mentioned in the introduction, the padding scheme used in the Merkle–Damgård construction must be chosen carefully to ensure the security of the scheme. Mihir Bellare gives sufficient conditions for a padding scheme to possess to ensure that the MD construction is secure: it suffices that the scheme be "MD-compliant" (the original length-padding scheme used by Merkle is an example of MD-compliant padding).[1]: 145 Conditions:
- is a prefix of
- If then
- If then the last block of is different from the last block of
Where denotes the length of . With these conditions in place, we find a collision in the MD hash function exactly when we find a collision in the underlying compression function. Therefore, the Merkle–Damgård construction is provably secure when the underlying compression function is secure.[1]: 147
Length padding example[edit]
To be able to feed the message to the compression function, the last block needs to be padded with constant data (generally with zeroes) to a full block. For example, suppose the message to be hashed is "HashInput" (9 octet string, 0x48617368496e707574 in ASCII) and the block size of the compression function is 8 bytes (64 bits). We get two blocks (the padding octets shown with lightblue background color):
- 48 61 73 68 49 6e 70 75, 74 00 00 00 00 00 00 00
This implies that other messages having the same content but ending with additional zeros at the end will result in the same hash value. In the above example, another almost identical message (0x48617368496e7075 7400) will generate the same hash value as the original message "HashInput" above. In other words, any message having extra zeros at the end makes it indistinguishable from the one without them. To prevent this situation, the first bit of the first padding octet is changed to "1" (0x80), yielding:
- 48 61 73 68 49 6e 70 75, 74 80 00 00 00 00 00 00
However, most common implementations use a fixed bit-size (generally 64 or 128 bits in modern algorithms) at a fixed position at the end of the last block for inserting the message length value (see SHA-1 pseudocode). Further improvement can be made by inserting the length value in the last block if there is enough space. Doing so avoids having an extra block for the message length. If we assume the length value is encoded on 5 bytes (40 bits), the message becomes:
- 48 61 73 68 49 6e 70 75, 74 80 00 00 00 00 00 09
Note that storing the message length out-of-band in metadata, or otherwise embedded at the start of the message is an effective mitigation of the length extension attack[citation needed], as long as invalidation of either the message length and checksum are both considered failure of integrity checking.
References[edit]
- Handbook of Applied Cryptography by Menezes, van Oorschot and Vanstone (2001), chapter 9.
- Introduction to Modern Cryptography, by Jonathan Katz and Yehuda Lindell. Chapman and Hall/CRC Press, August 2007, page 134 (construction 4.13).
- Cryptography Made Simple by Nigel Smart (2015), chapter 14.
- ^ a b c d Goldwasser, Shafi; Bellare, Mihir (July 2008). "Lecture Notes on Cryptography". Archived from the original on 2021-07-14. Retrieved 2023-03-28.
- ^ R.C. Merkle. Secrecy, authentication, and public key systems. Stanford Ph.D. thesis 1979, pages 13-15.
- ^ R.C. Merkle. A Certified Digital Signature. In Advances in Cryptology – CRYPTO '89 Proceedings, Lecture Notes in Computer Science Vol. 435, G. Brassard, ed, Springer-Verlag, 1989, pp. 218-238.
- ^ I. Damgård. A Design Principle for Hash Functions. In Advances in Cryptology – CRYPTO '89 Proceedings, Lecture Notes in Computer Science Vol. 435, G. Brassard, ed, Springer-Verlag, 1989, pp. 416-427.
- ^ Kelsey, John; Schneier, Bruce (2004). "Second Preimages on n-bit Hash Functions for Much Less than 2^n Work" (PDF) – via Cryptology ePrint Archive: Report 2004/304.
{{cite journal}}: Cite journal requires|journal=(help) - ^ Antoine Joux. Multicollisions in iterated hash functions. Application to cascaded construction. In Advances in Cryptology – CRYPTO '04 Proceedings, Lecture Notes in Computer Science, Vol. 3152, M. Franklin, ed, Springer-Verlag, 2004, pp. 306–316.
- ^ John Kelsey and Tadayoshi Kohno. Herding Hash Functions and the Nostradamus Attack In Eurocrypt 2006, Lecture Notes in Computer Science, Vol. 4004, pp. 183–200.
- ^ Stevens, Marc; Lenstra, Arjen; de Weger, Benne (2007-11-30). "Nostradamus". The HashClash Project. TU/e. Retrieved 2013-03-30.
- ^ Yevgeniy Dodis, Thomas Ristenpart, Thomas Shrimpton. Salvaging Merkle–Damgård for Practical Applications. Preliminary version in Advances in Cryptology – EUROCRYPT '09 Proceedings, Lecture Notes in Computer Science Vol. 5479, A. Joux, ed, Springer-Verlag, 2009, pp. 371–388.
- ^ Thai Duong, Juliano Rizzo, Flickr's API Signature Forgery Vulnerability, 2009
- ^ Lucks, Stefan (2004). "Design Principles for Iterated Hash Functions" – via Cryptology ePrint Archive, Report 2004/253.
{{cite journal}}: Cite journal requires|journal=(help) - ^ Mridul Nandi and Souradyuti Paul (2010). "Speeding Up the Widepipe: Secure and Fast Hashing" - via Cryptology ePrint Archive, Paper 2010/193
- ^ Sarkar, Palash; Schellenberg, Paul J. (2001). A parallel algorithm for extending cryptographic hash functions. Lecture Notes in Computer Science. Vol. 2247. Springer-Verlag. pp. 40–49. doi:10.1007/3-540-45311-3_4. ISBN 978-3-540-45311-6.
- ^ Pal, Pinakpani; Sarkar, Palash (2003). PARSHA-256 – A new parallelizable hash Function and a multithreaded implementation. Lecture Notes in Computer Science. Vol. 2887. Springer-Verlag. pp. 347–361. doi:10.1007/978-3-540-39887-5_25. ISBN 978-3-540-39887-5.











